In my previous articles I have demonstrated how to enable Azure Arc for on premises machines, put the Azure Monitoring Agent on those machines. For my last article in this series, I will be setting up the Security Events to flow into Sentinel using Data Collection Rules. Enough of that, let’s get into this.
Before I start the walk through, I want to discuss very briefly why the Azure Monitoring Agent is better than the current Microsoft Monitoring Agent which will be going EOL on August 31, 2024. From my standpoint its better because you can get granular with what you want to collect. The MMA you can only collect All, Common, Minimal. The AMA agent not only can you do those you can also collect specific event ID’s by using XPaTH queries. This can be great to aid in cutting down the noise and or the amount of data ingested. I will demonstrate this process in another post.
Once you have the machine onboarded with the Azure Monitoring go into Sentinel Data Connectors and search for Windows Security Events with AMA

Click on the data connector and then click Open Connector Page

Click on Create Data Collection Rule
Fill out the form, I usually put the Data Collection Rule in the same Resource Group as Sentinel

Click on the Resources Tab
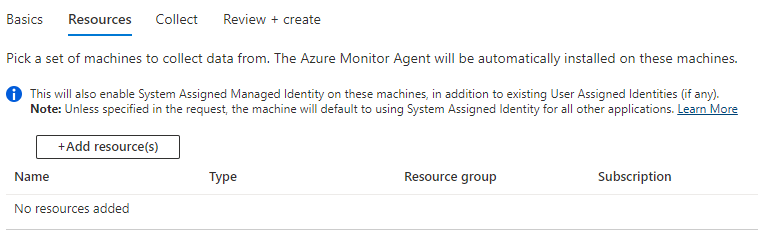
Click on Add Resources, you can then select the resources you want to add to this rule. Once you select the servers, click on Apply


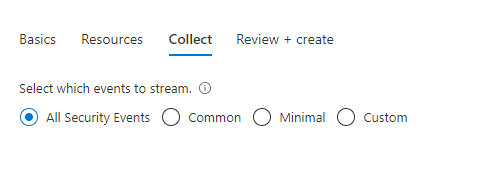
Click on the Collect Tab, and then custom
Click on Review and Create, then Create
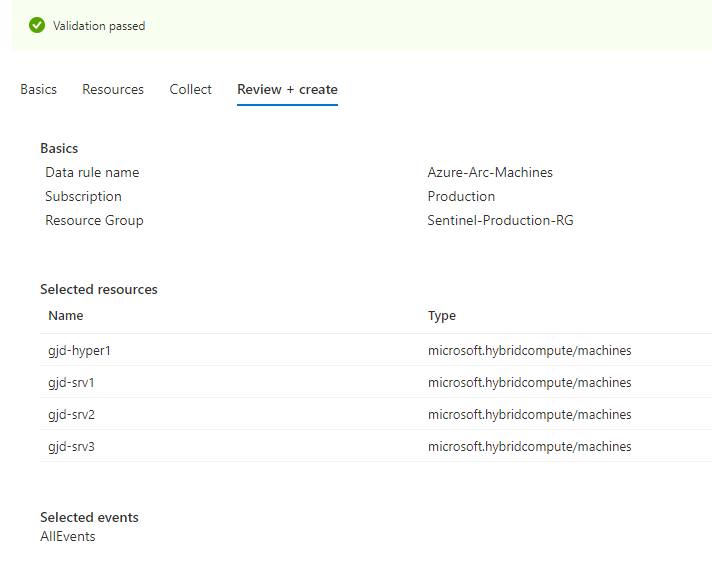
Now you have enabled Windows Security Events to be ingested into Sentinel using the Azure Monitoring Agent.