In this article I am going to walk you though how to do XPath queries to be used to ingest Windows Security Events into Sentinel
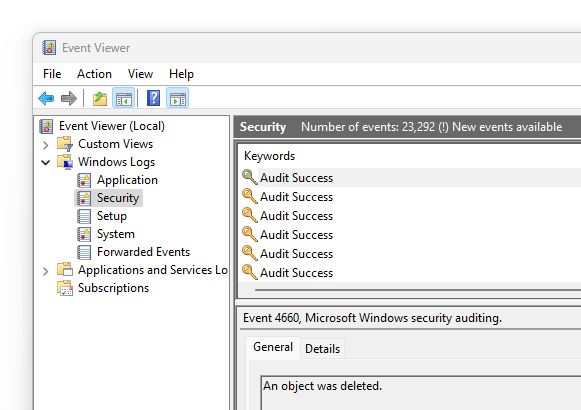
First step is to open up event viewer, honestly on any windows machine it will work. In this example we are going to gather Logon and Logoff events
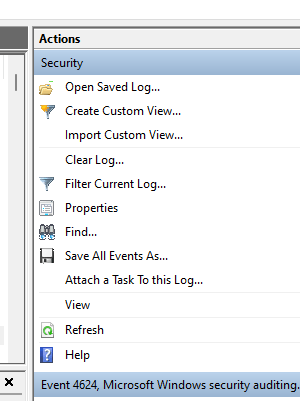
Click on Filter Current Log on the right of the Event viewer
The following screen will come up

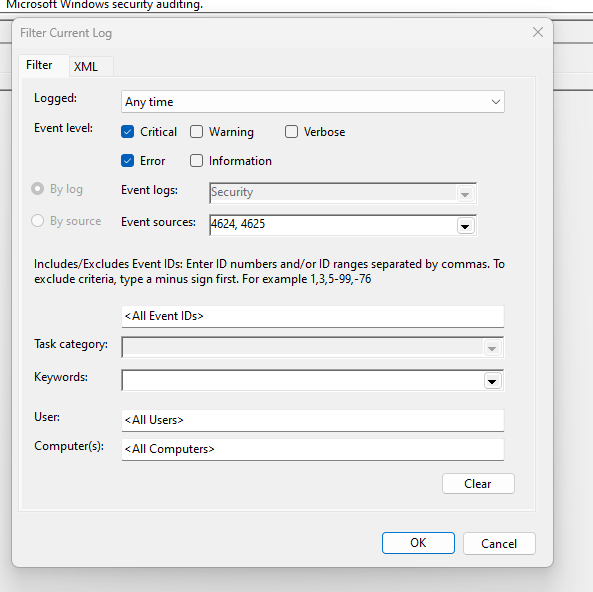
Once you do that, click on the XML tab
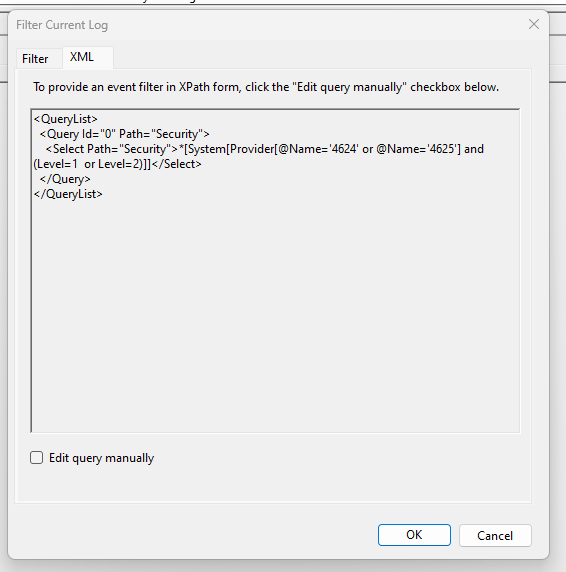
You will note you only need the following section of the XML statement.
“Security”>*[System[Provider[@Name=’4624′ or @Name=’4625′] and (Level=1 or Level=2)]]
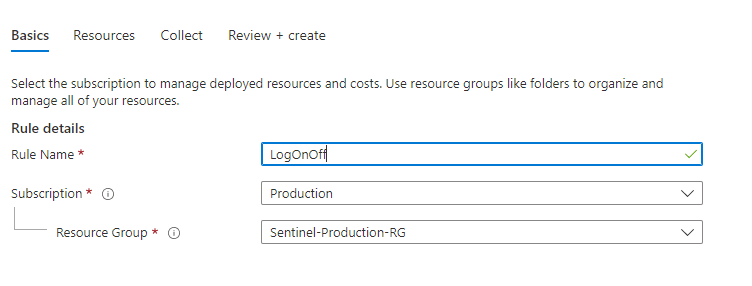
Now that you have your XPATH Open up the data connector for Windows Security Events via AMA. Click on the Create Data Collection Rule and fill out the Basics
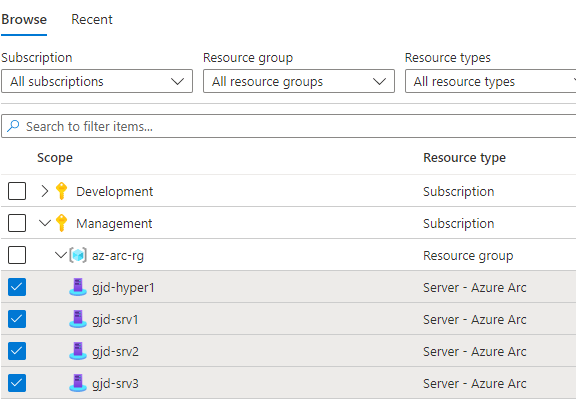
Click on Resources tab, click on Add Resources and click Apply
Click on the Collect Tab
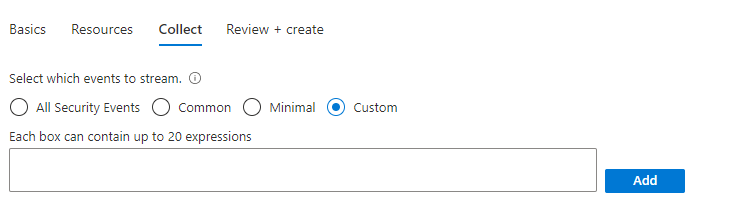
Paste in the XPATH into the box and click Add

Click on the Review and Create

Click on Create

I think you might need to remove the “>”
LikeLike