I was currently working in my lab and in Sentinel. I was looking over my current workspace usage and noticed that Azure Diagnostic was my top ingestion and I wanted to remove the data connector to stop the ingestion. The specific data connector that was enabled to cause this situation was the Network Security Groups. Enough of that, now lets get into it.
First let’s review the Data Connector in question, Network Security Groups. In order for this data connector to be enabled you go through the process to create an Azure Policy. Once you go through the process it points the specified NSG’s to a specific Log Analytics Workspace.
Once the policy has been deployed in polices it will look like the following example.
Next let’s look at the diagnostic settings for the NSG.
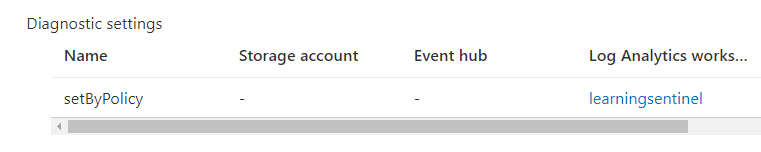
Notice how the diagnostic settings is setByPolicy. From a manual aspect you could just delete this setting and it will stop sending diagnostic data to my Log Analytics Workspace, but that is too easy.
Another fellow customer engineer sent me a link to a great article and an awesome script that will pull which resources have the diagnostic settings enabled. The script and the article can be found here. I also created a direct link to my repo that has the script, it can be found here.
Run the script in your Azure environment and it will produce a CSV list of all the Azure resources that have the diagnostic settings enabled. In file you will need the following information.
- Policy Name
- Resource ID of resource you want to change
- Workspace ID of the workspace you are wanting to change
The powershell module you will be utilizing is Set-AzDiagnosticSetting, below is an example
Set-AzDiagnosticSetting -Name "PolicyName" -ResourceId "ResourceID" -WorkspaceId "WorkSpaceID" -Enabled $False
Run the script and the setting will be removed. If you have a large environment that you need to do this for multiple resources you could do some advanced scripting to loop through a list.
I hope this will help you out. Have a great day.